Just write, take notes
MISC24-25
Change the picture height to see the flag
MISC26
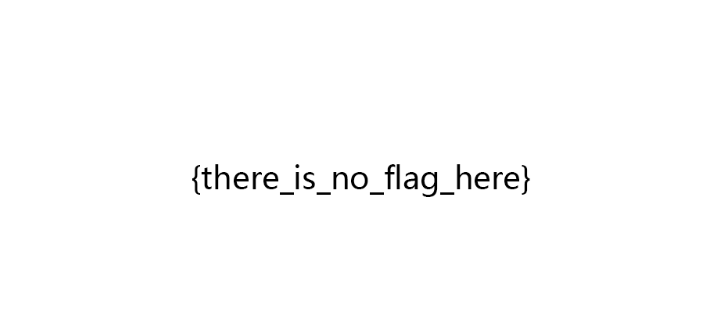
The title suggests that the flag is under the picture, but how many are there?
Change the height to 900 and you can see half of the flag:
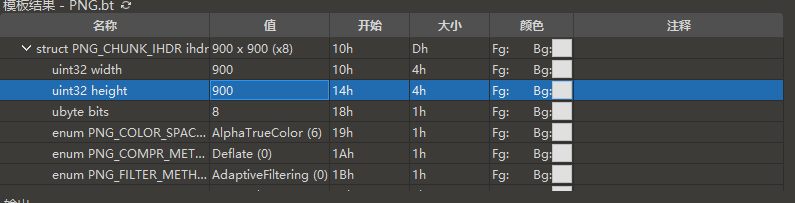
Here we also need to find out the real height of this picture and see the script of the boss on the Internet:
import binascii
import struct
crcbp = open("misc26.png", "rb").read()
for i in range(2000):
for j in range(2000):
data = crcbp[12:16] + struct.pack('>i', i)+struct.pack('>i', j)+crcbp[24:29]
crc32 = binascii.crc32(data) & 0xffffffff
if(crc32 == 0xEC9CCBC6):
print(i, j)
print('hex:', hex(i), hex(j))
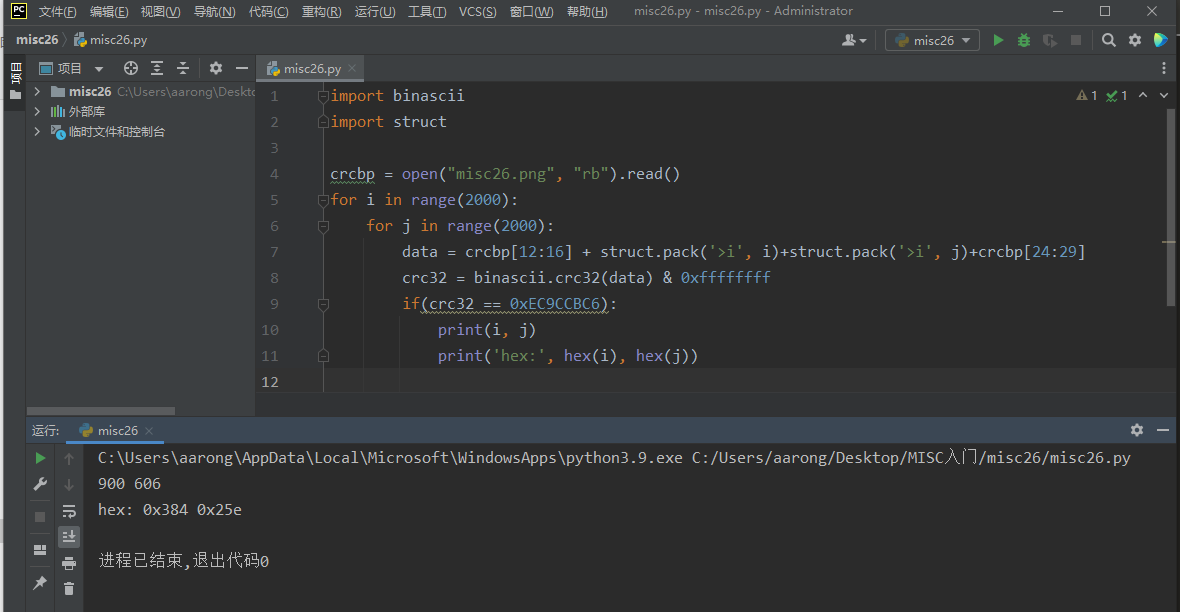
Width is 0x384 and height is 0x25e (HEX)
So the real height is 25e. Splice this into the flag to get the correct flag
MISC28
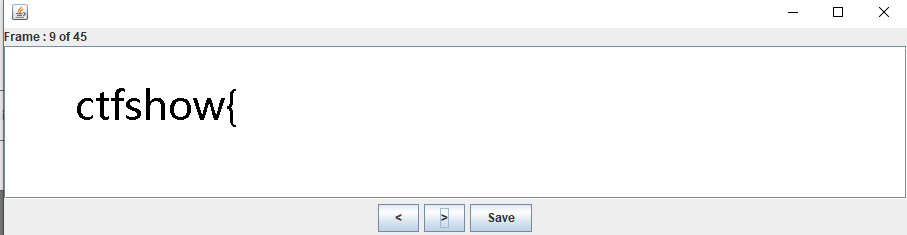
If the title is a gif file
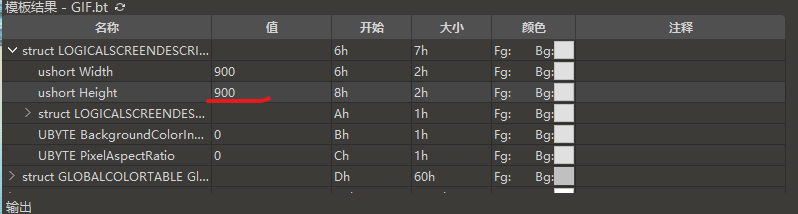
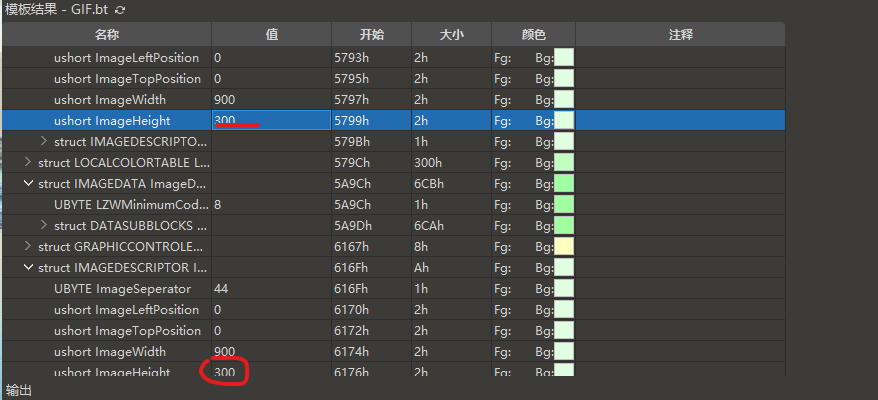
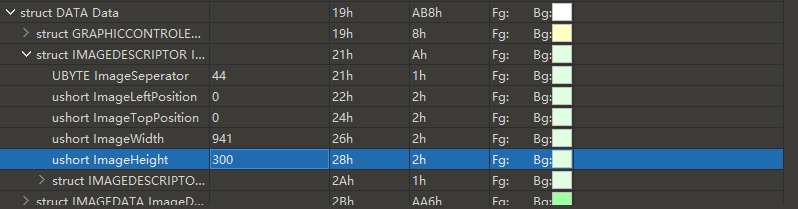
Open it with 010 Editor, change the height of the picture to 300, and save it
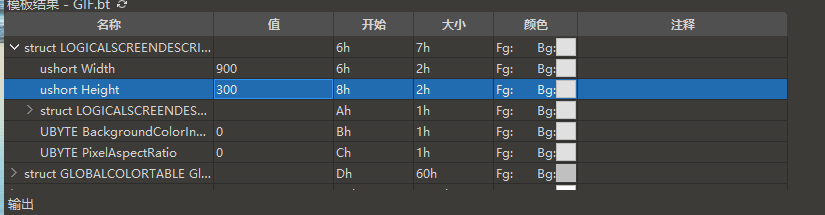
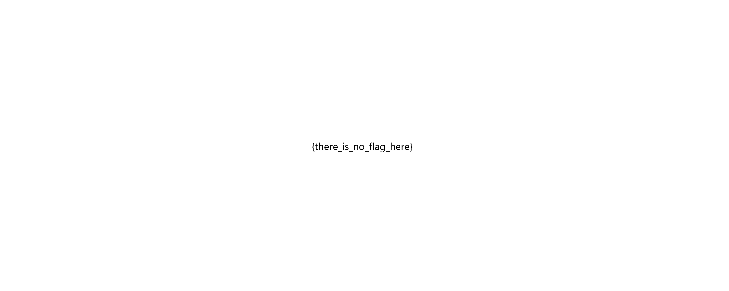
Open the picture and no flag appears
Try again to change the height to 900. It may not be enough:
Save or open the picture without a flag:
Then it may not be to modify the height of this image, and then look for the height of the image in the following analysis package:
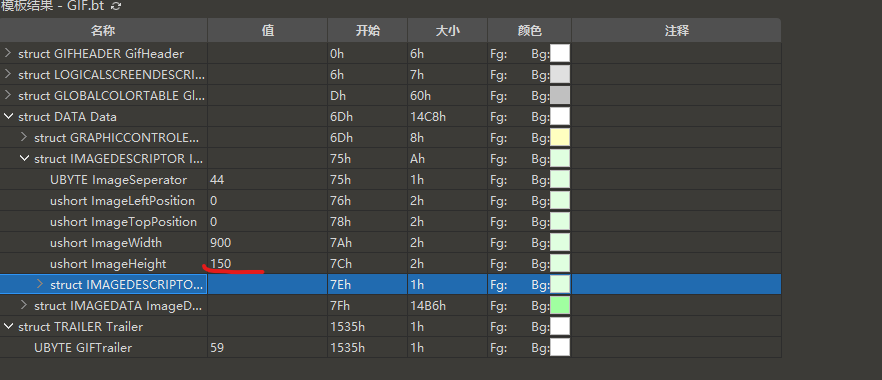
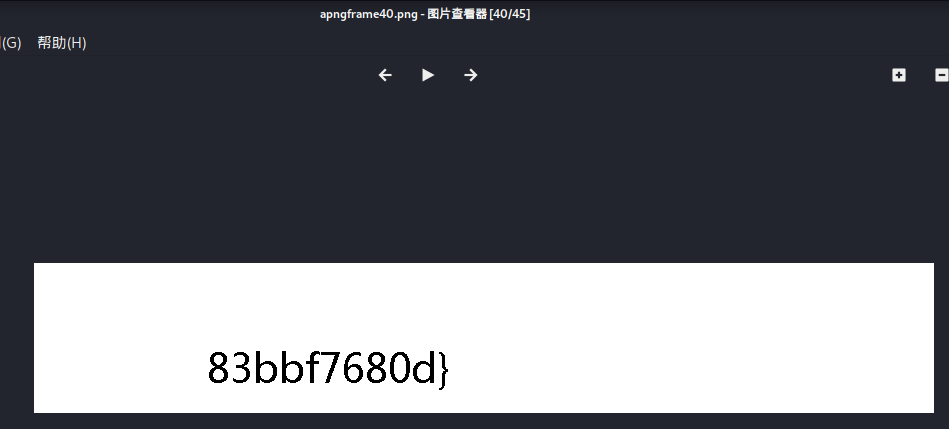
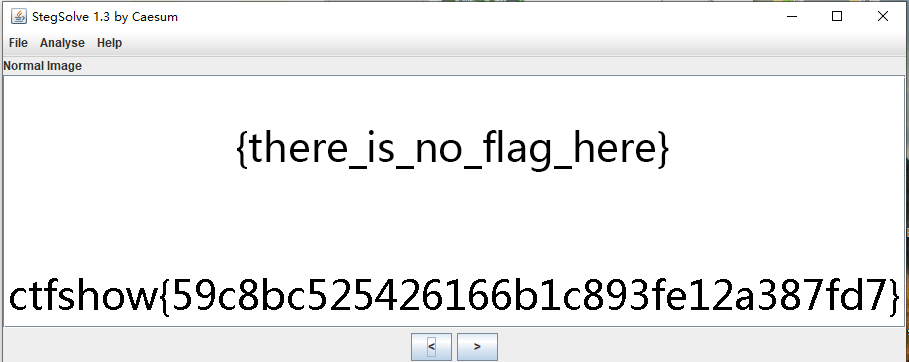
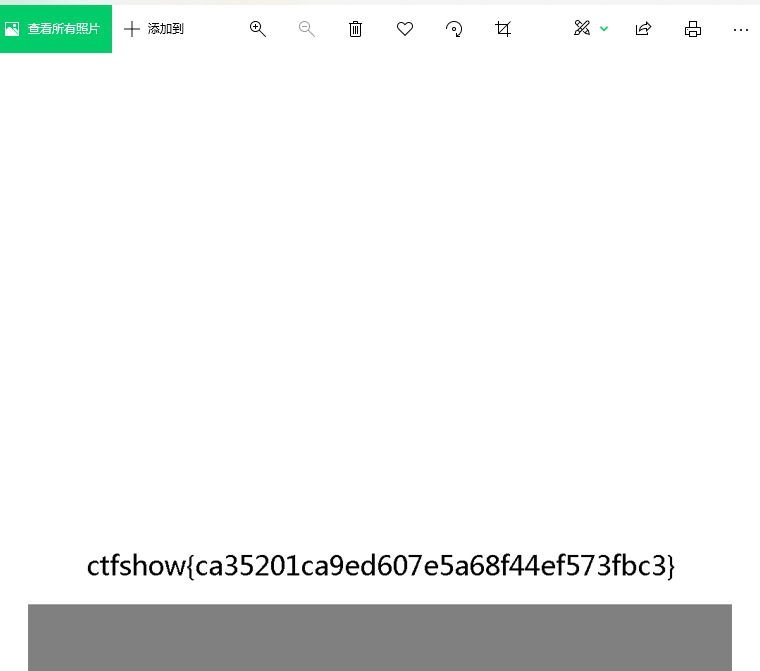
Try changing the height and save it to see the flag. Maybe this frame plays faster. You can use slide show pause or stepsolve to view it:
MISC29
The same as the question is a gif picture
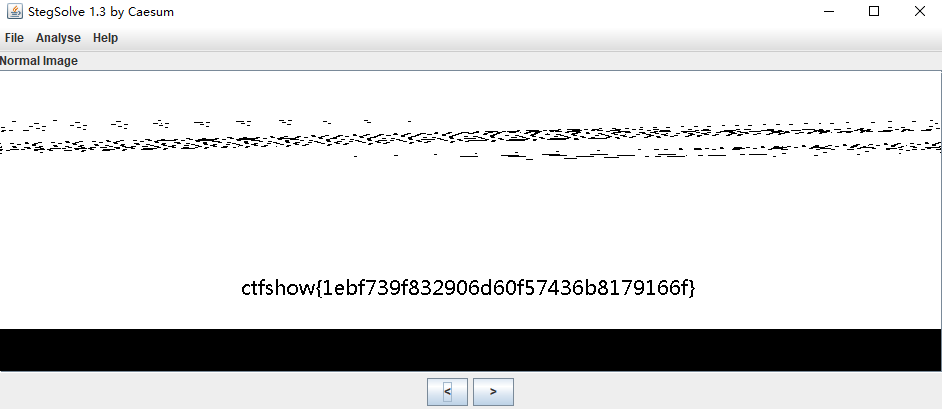
First analyze the number of frames with stepsolve and find that there are ten frames in this picture:
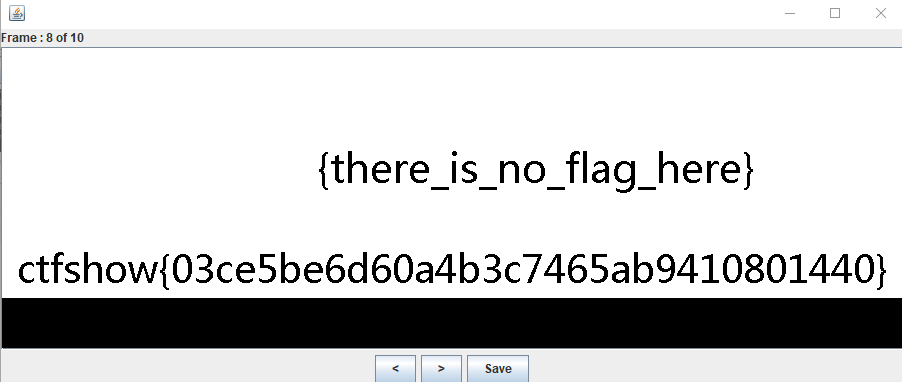
Change the height of these ten frames to 300, and find the flag in the eighth frame:
MISC30
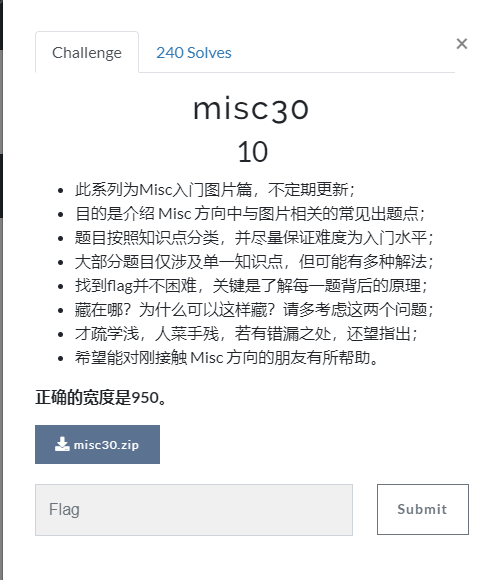
Open the picture and paste it into a ball. The correct width of the title prompt is 950. Try to modify it first to get the flag directly.
MISC31
Tip: the height is correct, but what is the correct width
Before doing this problem, you should first learn about bmp pictures Relevant knowledge.
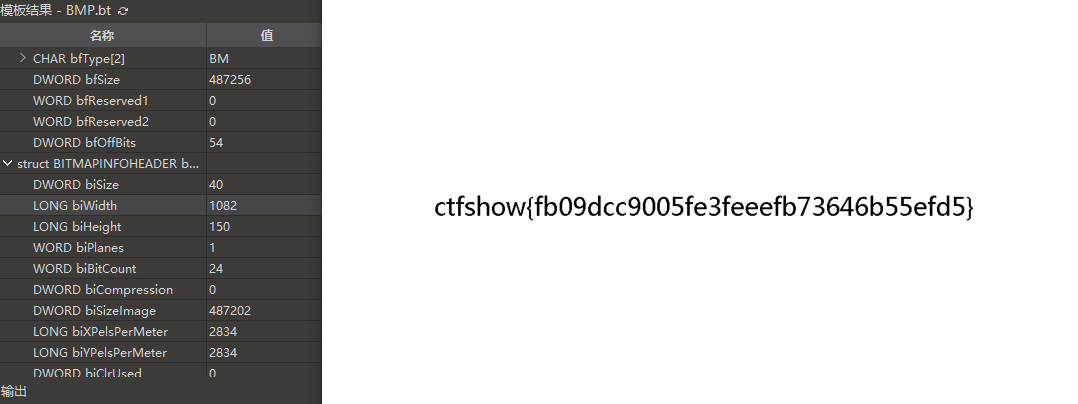
Check the specific information of the picture first:
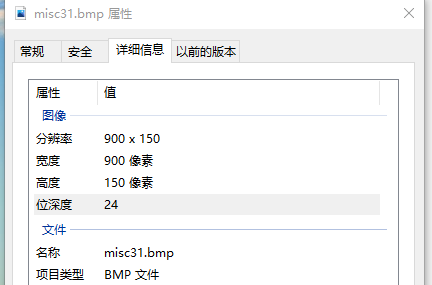
By analyzing this picture, it is easy to know that the end of the file is 0x76F50, and the file header occupies 53 bytes. One 00 is automatically supplemented by windows system, so it is not included. 76F50 is converted to decimal 487248
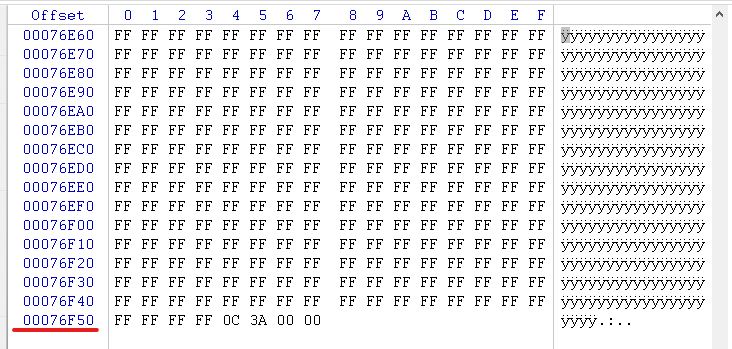
Therefore, according to the structure of bmp picture, the calculation formula can be obtained: (487248-53) / (3 * 150) ≈ 1082
So change the width to 1082 to get the flag.
MISC32
This question is the same as question 26. You can use the script run of question 26. Just change the path and crc value of the picture:
I didn't know much about CRC verification at the beginning. I found several materials and learned that CRC is cyclic redundancy verification code: it is the most commonly used error checking verification code in the field of data communication. Its feature is that the length of information field and verification field can be selected arbitrarily. Cyclic redundancy check (CRC) is a data transmission error detection function, which performs polynomial calculation on the data and attaches the obtained results to the back of the frame. The receiving equipment also executes similar algorithms to ensure the correctness and integrity of data transmission.
Here I give several blog posts about the height and width obtained by crc blasting: 1,2,3 Can understand relevant knowledge.
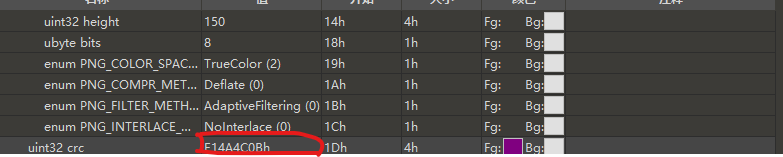
The crc value of the obtained picture is 0xE14A4C0B
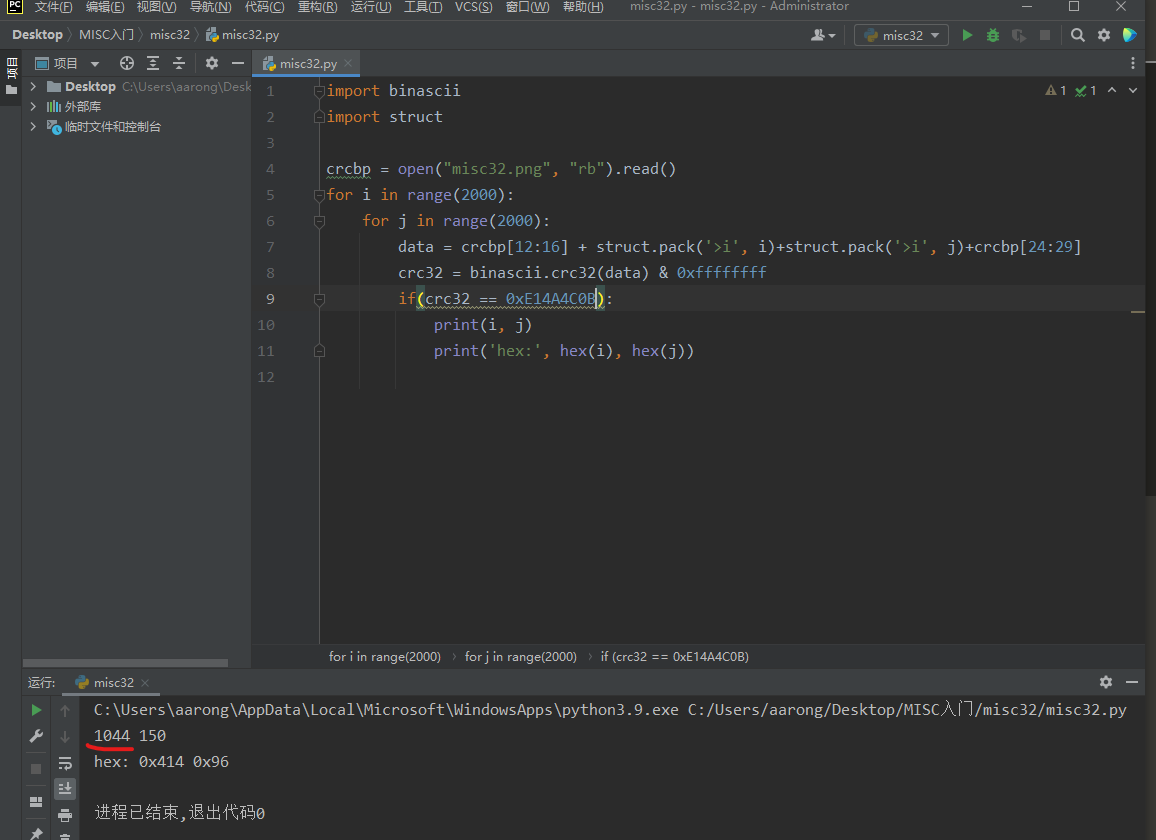
The width of the picture should be 1044, and the flag can be obtained by changing the height.
MISC33
This time, the height and width are required, or use the above script to explode the crc
Find the crc value of the picture first:
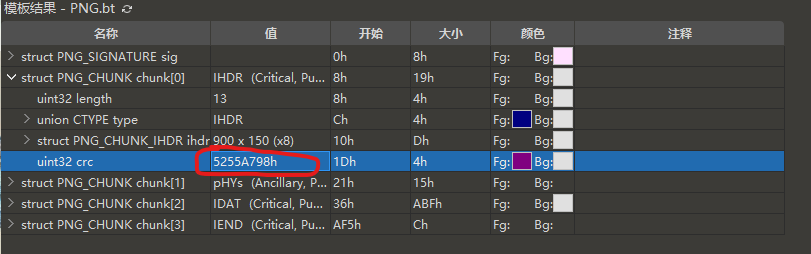
Then use the script run to get the width of 978 and the height of 142. Change the height and width of the picture to get the flag
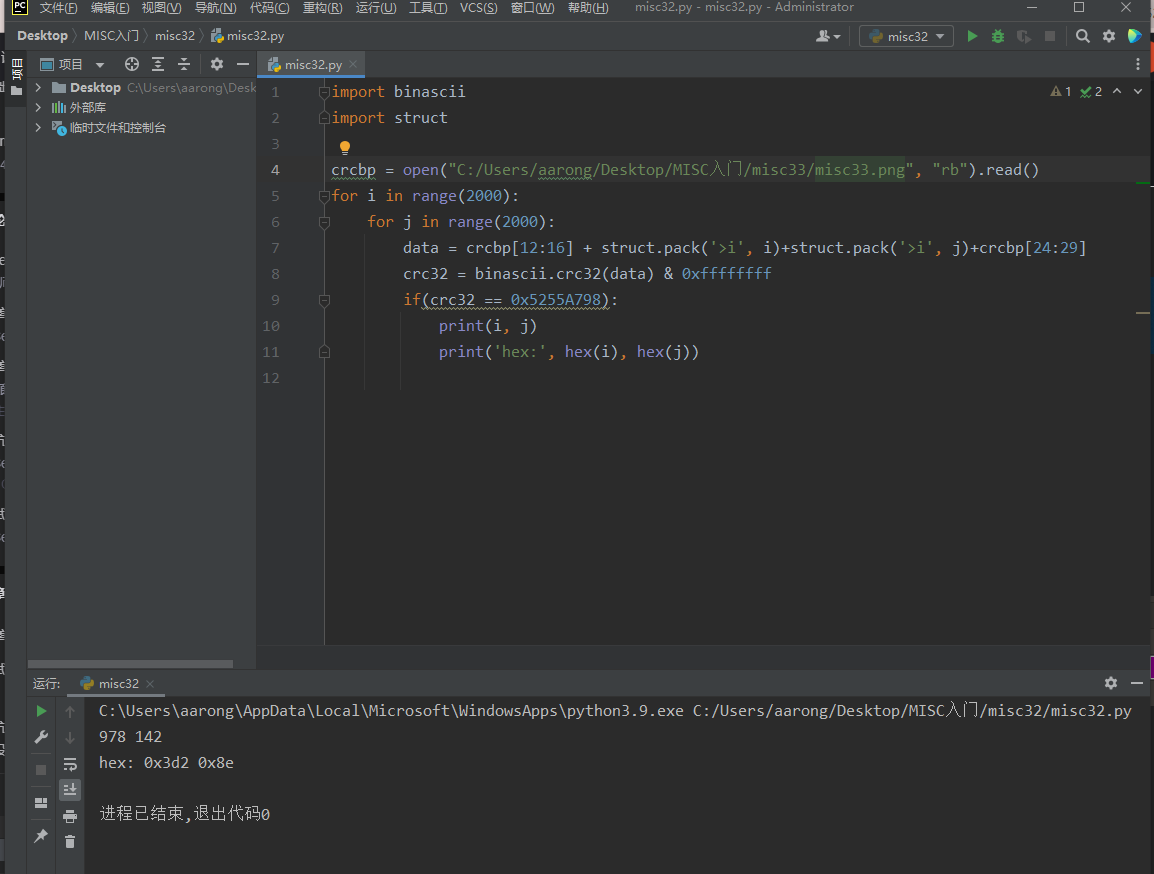
MISC34
Tip: the author jumped over the wall and changed the CRC of IHDR block, but we know that the correct width must be greater than 900
Give the script directly:
import zlib
import struct
filename = "misc34.png"
with open(filename, 'rb') as f:
all_b = f.read()
w = all_b[16:20]
h = all_b[20:24]
for i in range(901,1200):
name = str(i) + ".png"
f1 = open(name,"wb")
im = all_b[:16]+struct.pack('>i',i)+all_b[20:]
f1.write(im)
f1.close()
One picture is separated, and flag is found in one of them:
MISC35
Tip: the person who created the question fought tenaciously, but we know that the correct width must be greater than 900
The script of the previous question is slightly modified:
import zlib
import struct
filename = "misc35.jpg"
with open(filename, 'rb') as f:
all_b = f.read()
w = all_b[159:161]
h = all_b[157:159]
for i in range(901,1200):
name = str(i) + ".jpg"
f1 = open(name,"wb")
im = all_b[:159]+struct.pack('>h',i)+all_b[161:]
f1.write(im)
f1.close()
MISC36
The same code is given:
import zlib
import struct
filename = "misc36.gif"
with open(filename, 'rb') as f:
all_b = f.read()
w = all_b[6:8]
for i in range(920,950):
name = str(i) + ".gif"
f1 = open(name,"wb")
im = all_b[:38]+struct.pack('>h',i)[::-1]+all_b[40:]
f1.write(im)
f1.close()
At 941 Modify height in GIF:
MISC37
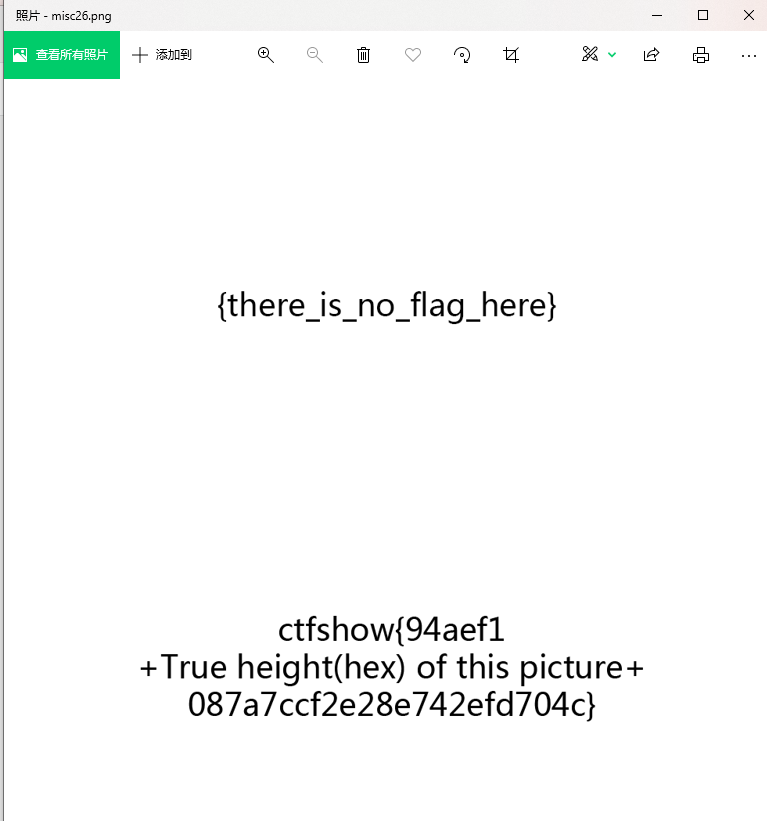
If the title is a gif picture, analyze it frame by frame to get the flag
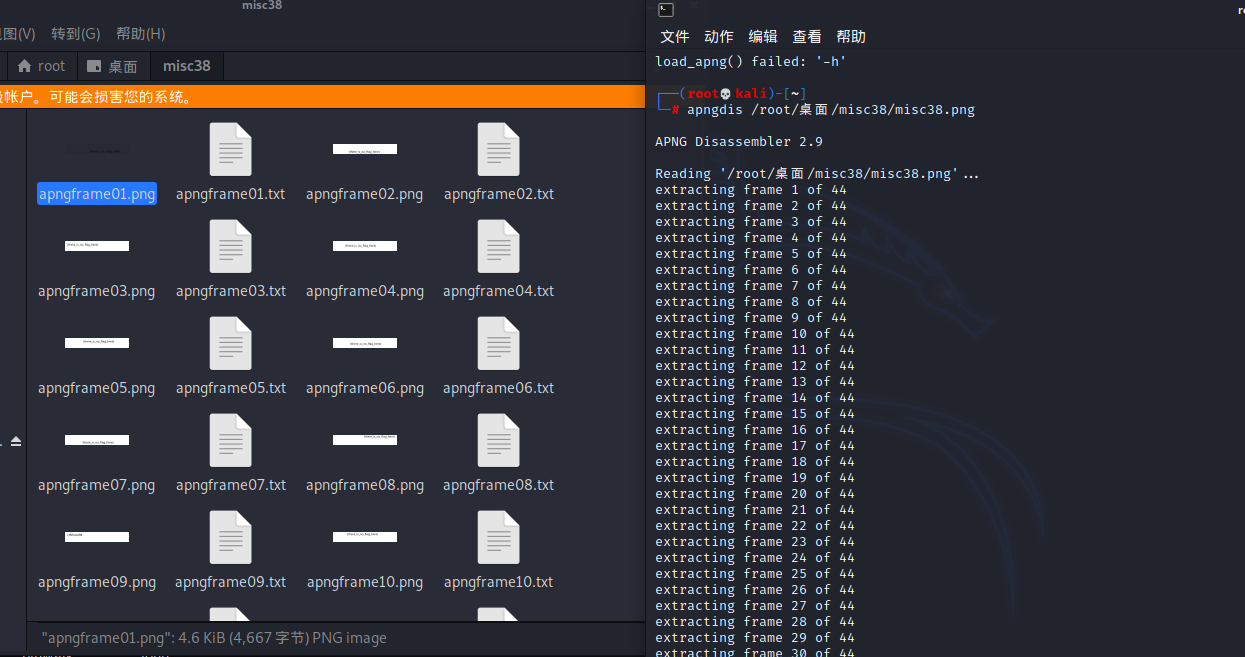
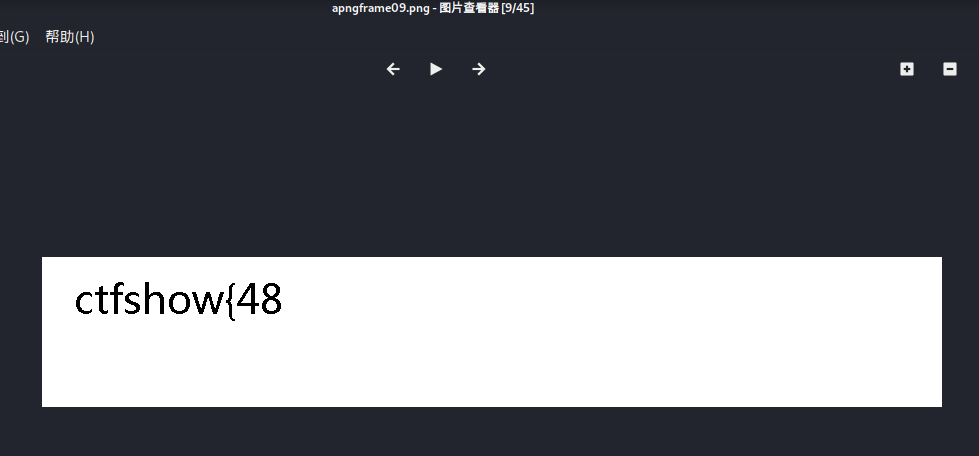
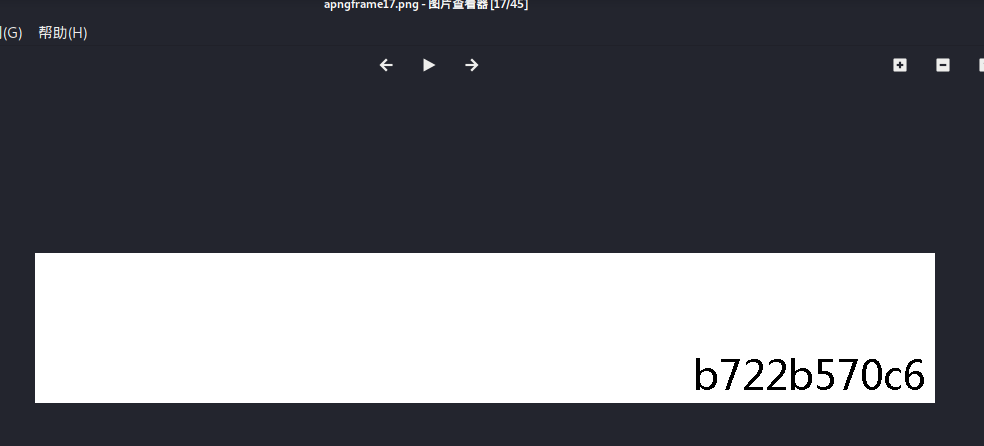
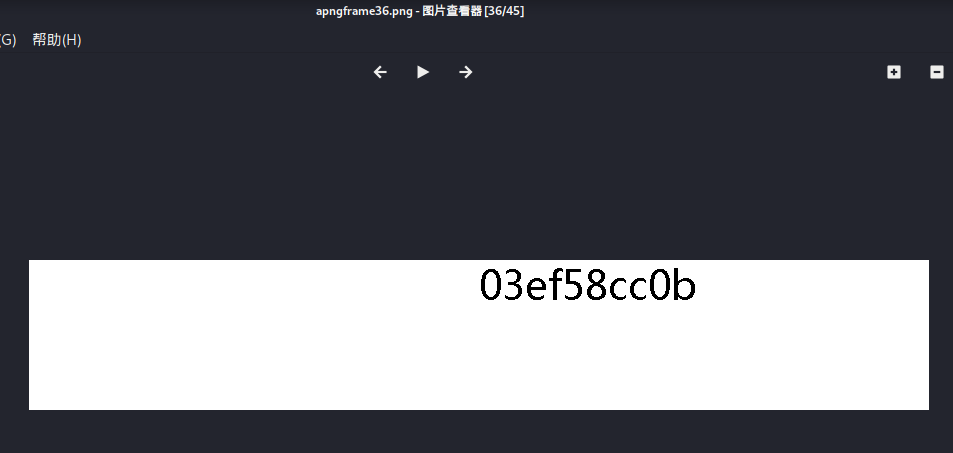
MISC38
Using apngdis(APNG Disassembler 2.9), kali can install and directly separate the pictures: