7, Figure
Basic concept of graph
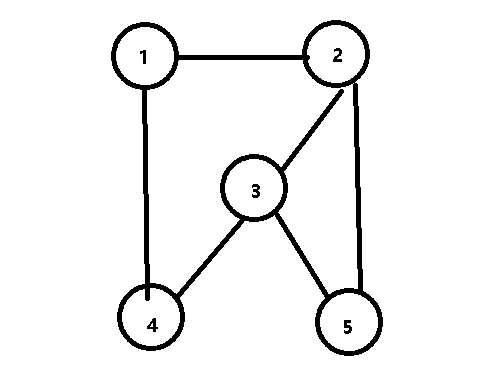
1. Graph: graph G is composed of two sets V and E, marked as G=(V,E), where V is a finite nonempty set of vertices and E is a finite set composed of ordered pairs of vertices in V. these ordered pairs are called edges or arcs
2. Undirected graph
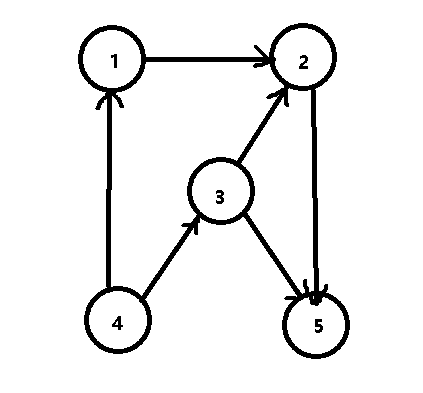
3. Directed graph
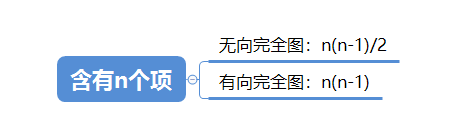
4. Complete graph: if there are edges between any two vertices, the graph is called undirected complete graph
At least the following edges exist (example):
5. Degree, in degree and out degree of vertex
Degree = in degree + out degree
TD(v) = ID(V) + OD(V)
Penetration: the number of arcs with vertex v as the head is called the penetration of V
Outgoing degree: the number of arcs ending at vertex v is called the outgoing degree of V
6. Subgraph
All vertices of a directed graph: sum of out degrees = sum of in degrees
7. Connected, connected graph and connected component
! Path ≠ edge
There is only one connected component of any connected graph, that is, itself;
For an undirected graph with n vertices, at least n-1 edges can be connected
8. Strongly connected graph and strongly connected component
Having n vertices requires at least n edges to be strongly connected
Storage of Graphs
Storage method: collar matrix, collar table, inverse collar table, cross linked list and collar multi table
1, Collar matrix (2D array)
Adjacency matrix: the matrix representing the relationship between nodes in the graph is called adjacency matrix
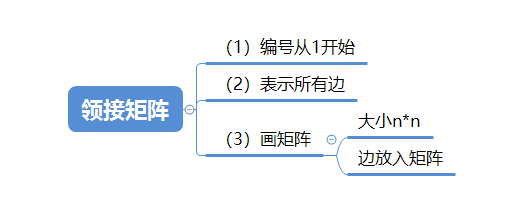
. features
(1) The collar matrix of an undirected graph is a symmetric matrix
(2) The number of nonzero elements in row i (or column i) of the collar matrix of an undirected graph is exactly the degree TD (Vi) of the ith vertex
(3) The number of nonzero elements in row i (or column i) of the collar matrix of a directed graph is exactly the out degree OD (Vi) (or in degree ID (Vi)) of the ith vertex
(4) Dense graphs are suitable for storage by collar matrix method
2, Collar table (storing the output of the graph) directed graph
Adjacency table: a table consisting of a vertex data table and edges (arcs) representing data relationships
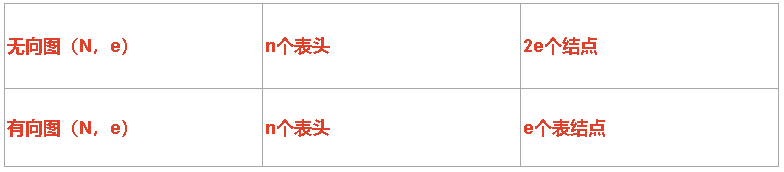
N: Vertex, e: edge
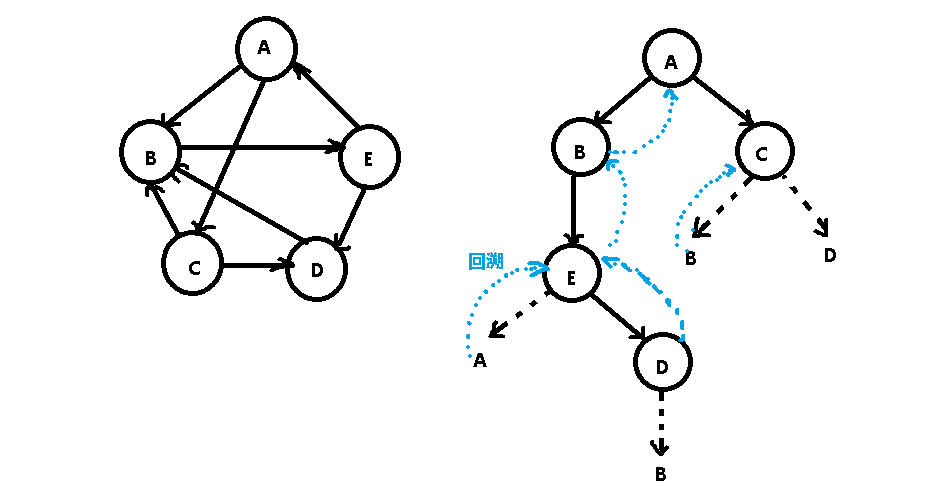
3, Traversal of Graphs
1. Breadth first search (BFS) visits a batch of nodes every time

2. Depth first search (DFS) goes to the end at one time, and if there is no way to go, go back
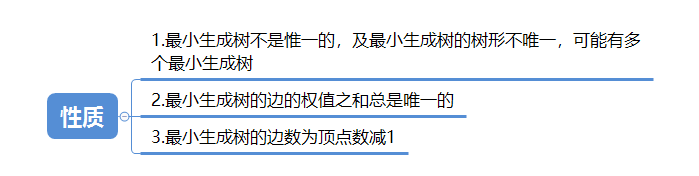
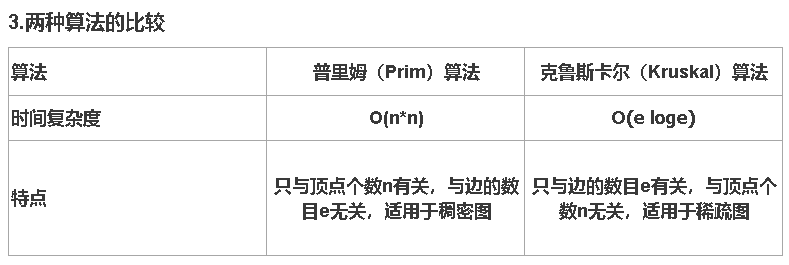
4, Minimum cost spanning tree
1.Prim algorithm (find the whole with the smallest weight)
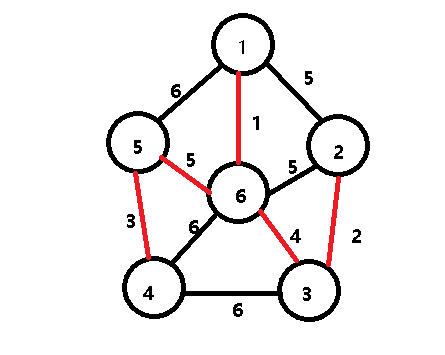
2.Kruskal algorithm (find the edge with the smallest weight until it is connected) is the same as above.
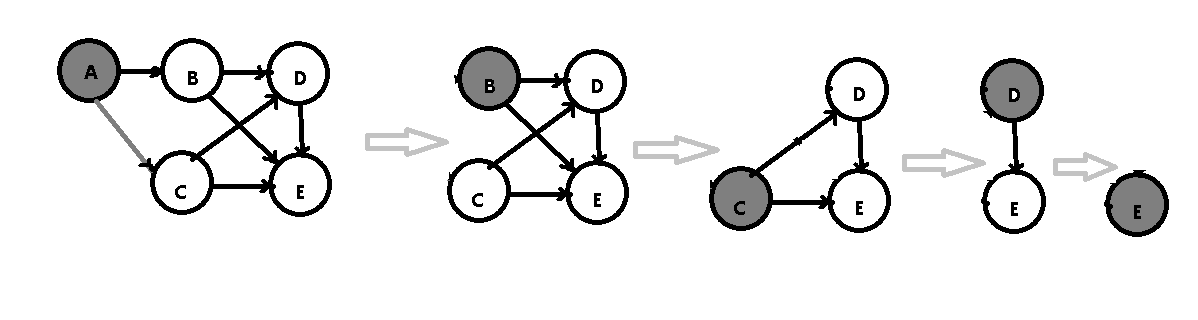
5, Topological sorting
Topological sorting: the operation of obtaining a total order on a set from a partial order on the set is called topological sorting
Premise: directed acyclic graph (DAG), that is, delete vertices with 0 degree each time and output them
Judgment question A graph with few edges is called a sparse graph,Otherwise, it is called dense graph(√) In a directed graph,The sum of in and out degrees of all vertices is equal to twice the number of edges.(√) Storage method of graph:adjacency matrix ,Adjacency table,Adjacency multiple table,Cross linked list and edge set array.(√) The depth first search of graph is similar to the first root traversal of tree(√) The breadth first search of graph is similar to the hierarchical traversal of tree.(√) choice question 1.The following statement about directed graph is correct? () A.Any vertex in a strongly connected graph has an arc to all other vertices B.A directed complete graph must be strongly connected C.The in degree of a vertex in a directed complete graph is equal to the out degree D.Subsets of edge sets and vertex sets of a directed graph can form subgraphs of the original graph answer: B 2.In a graph, the sum of the degrees of all vertices is equal to the sum of the degrees of all edges__Times () A.1/2 B.1 C.2 D.4 answer: C 3.A connected graph with 100 vertices needs at least () edges? A.99 B.100 C.101 D.102 answer: A
8, Search
1. Search: according to the value of the given keyword, search whether a data element equal to the value is in the search table. If it is found, the search is successful, and if it is not found, the search fails
2. Average search length (ASL):
The search length refers to the number of keywords to be compared, and the average search length is the average of the number of keyword comparisons in all search processes
ASL = total search times / number of elements
1, Sequential search
The average search length of sequential search is ASL = n+1/2
2, Half search
The average length of half search is ASL = log2 (n+1)
Binary sort tree: left subtree < root < right subtree
The code is as follows (example)
BstTree BstSearch(BstTree bst,DataType x){
if(bst==Null)
return Null;
else if(bst->data==x) //Root = = x
return bst;
else if(x<bst->data) //X < root
return BstSearch(bst->lchild , x); //Find left subtree
else(x>bst->data) // x> Root
return BstSearch(bst->rchild , x) //Find right subtree
}
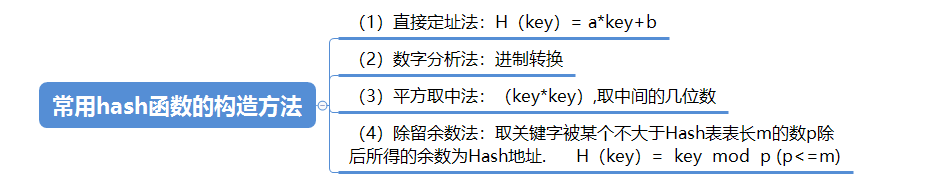
Hashtable
1. Construction methods of common hash functions
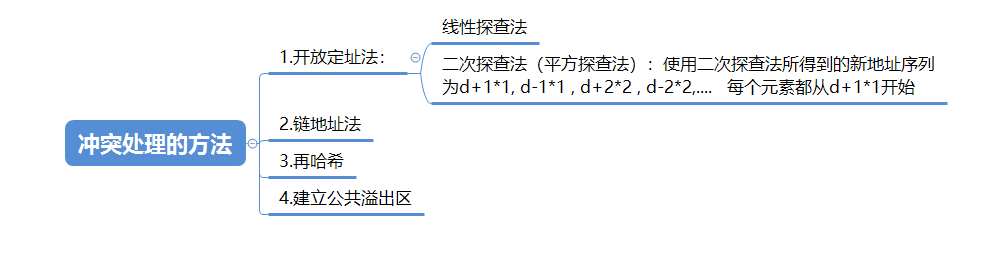
2. Conflict handling methods
Multiple choice questions 1.The construction methods of hash function are () A.direct addressing B.Digital analysis C.Square middle method,Folding method D.Division residue method and random number method answer: ABCD 2.The hash function handles conflicts by () A.Open address method B.double hashing C.Chain address method and establishing a public overflow area. D.Square middle method answer: ABC Judgment question A lookup table is a collection of data elements or records of the same type.(√) Static lookup table queries whether a specific data element is in the lookup table,Various attributes of a specific data element can be retrieved.(√) The dynamic lookup table inserts data elements that do not exist during the lookup process,Or you can delete an existing data element from the lookup table..(√) Two different keywords,Its hash function value is the same,Therefore, the phenomenon of being mapped to the same table location is called conflict.(√)
9, Sort
1. Sorting: it is an operation to arrange the records in the file at one time according to the increasing or decreasing order of keyword value, which can turn an unordered file into an ordered file
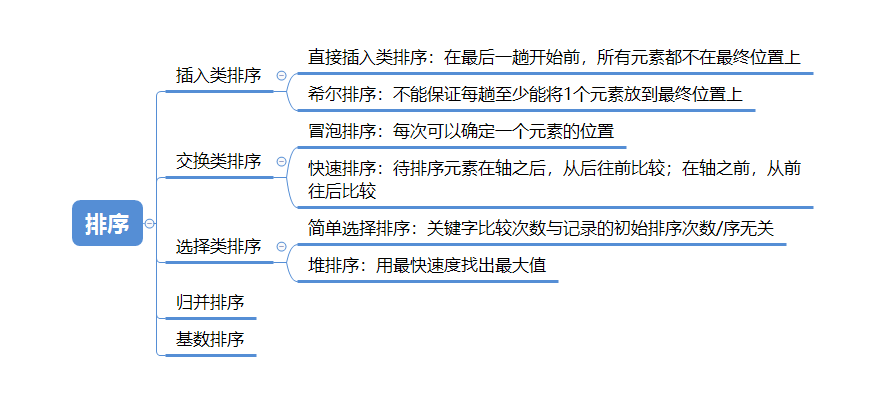
Stability of sorting algorithm: if the relative position of the same element before and after sorting does not change, it is stable, otherwise it is unstable
Internal sorting: in the sorting process, all records to be sorted are placed in memory for sorting, which is called internal sorting
External sorting: when there are many records to be sorted, not only memory but also external memory should be used for sorting. The sorting method is called external sorting
Comparison of various sorting methods
